Feedly for Threat Intelligence
Monitors and analyzes threat intelligence from thousands of security sources using AI to prioritize risks.
Are you the owner?
Claim this tool to publish updates, news and respond to users.
Sign in to claim ownership
Sign InDescription
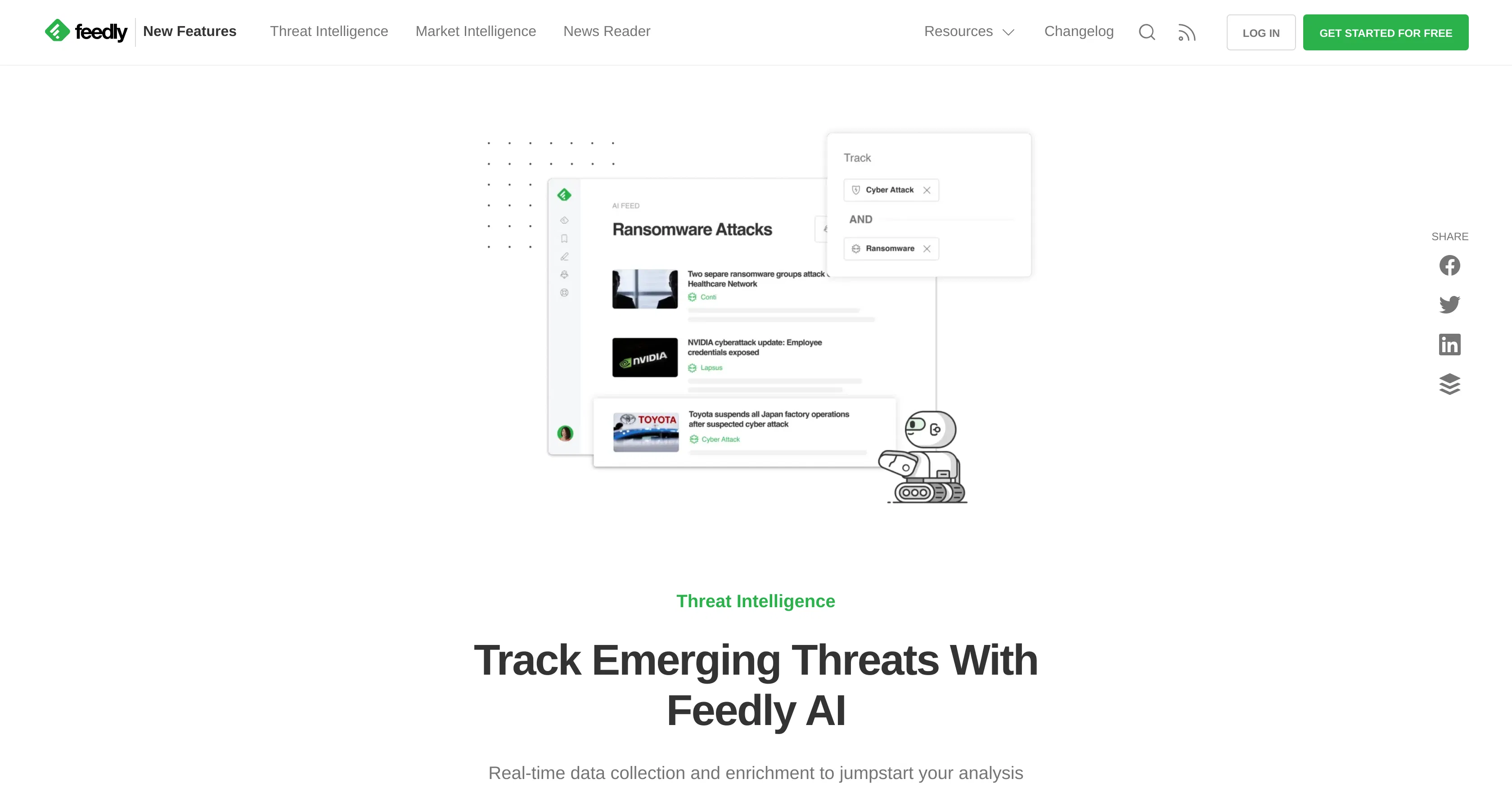
Feedly for Threat Intelligence, known as Feedly Leo, is an AI-powered platform developed by Feedly that aggregates and analyzes open-source threat intelligence from thousands of security blogs, news sites, and research reports. Its core value lies in helping security teams cut through the noise of information overload by using machine learning models to identify, track, and prioritize relevant threats, vulnerabilities, and threat actors, thereby accelerating threat detection and response times.
Key features: The platform continuously monitors a vast array of curated security sources, including vendor blogs, government alerts, and dark web forums. It employs AI models to automatically categorize and tag threats by type, such as malware, ransomware, or APT groups. Users can set up custom alerts for specific indicators of compromise (IoCs), vulnerabilities (CVEs), or threat actors. The system also provides contextual analysis and summaries of complex threats, highlighting potential impact and related campaigns to streamline analyst workflows.
What makes it unique is its focus on actionable intelligence rather than raw data feeds; the AI learns user priorities to surface the most critical information. Technically, it leverages natural language processing (NLP) and entity recognition to extract and link key security concepts. It operates as a cloud-based web application with mobile apps, offering integrations via API with popular security orchestration platforms like Slack, Microsoft Teams, and SIEM tools for automated alerting and workflow enrichment.
Ideal for security analysts, threat intelligence teams, and CISOs in organizations of all sizes who need to stay ahead of emerging cyber threats. Specific use cases include proactive vulnerability management by tracking newly disclosed CVEs, monitoring for brand impersonation or data leaks, conducting research on specific adversary tactics, and providing briefings on the evolving threat landscape to support strategic security decisions.
Similar Tools